
The landscape of cybersecurity is rapidly evolving with the integration of artificial intelligence. AI-driven tools enhance the ability to detect and respond to threats, providing organizations with robust protection against a wide range of cyber risks. This article explores the best AI cybersecurity tools available in 2026. It outlines key features, benefits, and challenges, as well as selection criteria for organizations looking to improve their security posture in a complex digital environment.
Best AI Cybersecurity tools in 2026
Darktrace
Darktrace takes a different approach to threat detection by focusing on what’s normal inside your network, rather than relying on known attack signatures. It uses AI to learn the behavior of every user, device, and system, and then flags anything that seems off. This makes it especially good at spotting novel or stealthy attacks that traditional tools might miss.
One standout feature is its autonomous response system, Antigena, which can take quick, precise action to contain threats — without shutting down your entire environment. That’s a huge plus for minimizing disruption during an incident.
That said, because it relies heavily on behavior modeling, it can sometimes be sensitive to legitimate but unusual activity, which may lead to false positives. Still, for businesses looking to defend against advanced or unknown threats, Darktrace offers a powerful, adaptive layer of protection.
Crowdstrike: AI native cybersecurity
CrowdStrike Falcon stands out for its massive-scale AI training, powered by telemetry from trillions of security events every week. This gives it the intelligence to spot and respond to complex attack patterns, particularly at the endpoint and container level, with impressive accuracy and low noise.
Its modular design is another strong point. You can add new features and defenses over time without having to overhaul your entire security setup — something that makes it scalable and future-proof.
Falcon excels at correlating data across users, devices, and workloads, which sharpens its ability to quickly detect and respond to threats. However, since it relies on IoC-based detection, it may be less tuned to pick up subtle, highly specific behavioral anomalies inside a single organization compared to tools that focus purely on internal baselines.
Still, for organizations looking for high-precision, globally informed endpoint protection, Falcon is a reliable and proven option.
SentinelOne
SentinelOne offers a strong, AI-driven platform through Purple AI, combining threat detection, analysis, and response into a single streamlined system. Its use of machine learning allows it to detect anomalies in real time by analyzing behavioral patterns, giving attackers less time to act.
One standout feature is its natural language interface, which makes threat hunting more accessible — allowing teams to ask questions and issue commands using everyday language. That lowers the barrier to using advanced capabilities.
The platform also shines in automated response, quickly executing actions to contain threats with minimal manual input. This not only speeds up reaction times but also helps reduce pressure on security teams, making SentinelOne a smart choice for organizations looking to scale their detection and response efficiently.
Command Zero: Autonomous & AI-assisted Cyber Investigations
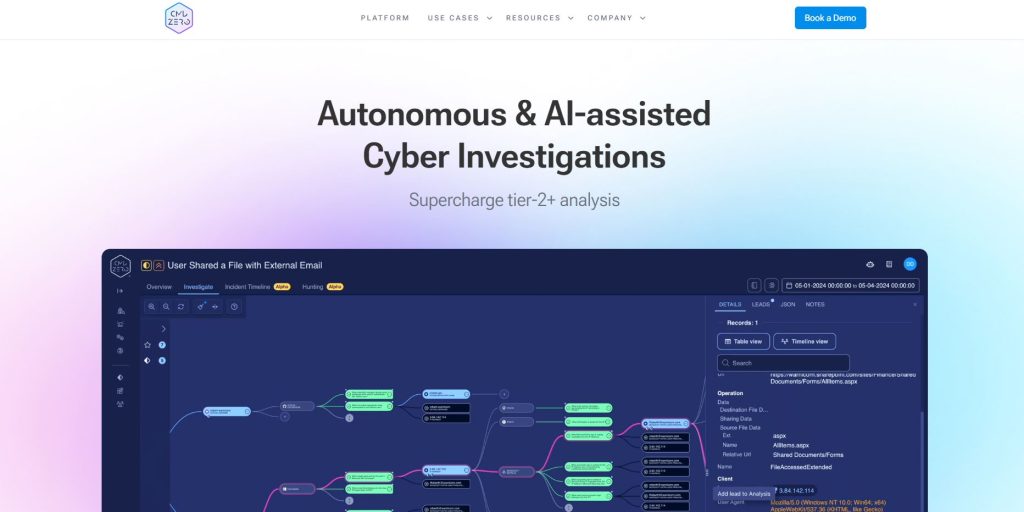
Command Zero uses AI to simplify and speed up cyber investigations, allowing security teams to focus on the cases that truly matter. Its automation reduces the manual workload, helping teams move faster and more efficiently through incidents.
A key strength is its autonomous investigation capability, which supports both user-led and fully automated workflows. This helps reduce delays in identifying and responding to threats.
Thanks to natural language processing, analysts can interact with the platform using plain English — no need for deep technical skills. That makes Command Zero especially valuable for teams looking to scale investigative work without adding complexity.
Overview of AI Cybersecurity Tools
The landscape of cybersecurity tools continues to evolve dramatically in 2026, driven by advancements in artificial intelligence technologies. Organizations are increasingly adopting AI-powered solutions to enhance their security measures and stay ahead of sophisticated threats.
Key Features of Top AI Security Solutions
Leading AI cybersecurity tools exhibit several essential features that set them apart. These include:
- Real-time Threat Detection: Continuous monitoring enables timely identification of potential threats, minimizing response delay.
- Automated Incident Response: Many tools offer capabilities to react autonomously to identified incidents, reducing the need for human intervention.
- Behavioral Analytics: Advanced algorithms analyze user and system behaviors to detect anomalies indicative of security breaches.
- Scalability: Effective tools are designed to scale up or down effortlessly, accommodating the needs of various organization sizes.
Benefits of AI-Driven Threat Detection and Response
AI-driven cybersecurity tools offer numerous advantages, making them indispensable for modern organizations. The primary benefits include:
- Increased Accuracy: Enhanced detection capabilities lead to a reduction in false positives, allowing security teams to focus on genuine threats.
- Proactive Threat Mitigation: AI tools can predict potential vulnerabilities based on historical data, enabling organizations to address weaknesses before they are exploited.
- Resource Optimization: Automation of routine security tasks frees up valuable personnel time, allowing human experts to concentrate on strategic initiatives.
Challenges in Implementing AI Cybersecurity Tools
While the benefits of AI cybersecurity tools are significant, organizations face various challenges in their deployment. Some key challenges include:
- Integration Difficulties: Implementing AI tools alongside existing security infrastructure can be complex and may require substantial adjustments.
- Data Privacy Concerns: The use of large datasets raises issues around data privacy and compliance with regulations.
- Dependence on Quality Data: The effectiveness of AI systems is reliant on the quality of the input data; poor data hampers their performance.
Best AI Tools for Cybersecurity: Selection Criteria
Selecting the right AI-driven cybersecurity tools is crucial for organizations aiming to enhance their defenses against evolving threats. Various criteria determine the effectiveness and efficiency of these tools in a complex cyber landscape.
Evaluating Detection Capabilities and False Positives
The primary function of any cybersecurity tool is to accurately detect threats while minimizing false positives. Effective solutions leverage advanced machine learning algorithms that analyze vast datasets for patterns indicative of malicious behavior. It’s essential to assess:
- Detection speed: How quickly the tool identifies potential threats.
- Accuracy: The percentage of correct detections compared to false alarms.
- Adaptability: Ability to learn from evolving threat landscapes to improve detection rates over time.
Integration with Existing Security Platforms and Systems
Seamless integration is vital for maximizing the effectiveness of AI cybersecurity tools. Solutions should work harmoniously with legacy systems and various security platforms to provide comprehensive protection. Aspects to consider include:
- APIs: Availability and ease of use for integrating with other security components.
- Interoperability: Compatibility with existing software and hardware systems.
- Data sharing: Ability to exchange data across platforms for enhanced threat visibility.
Scalability for Large Enterprises and Hybrid Cloud Environments
The ability to scale effectively is a key criterion when evaluating AI tools. Organizations should look for solutions that can grow as their infrastructure expands, especially in hybrid cloud setups. Key considerations include:
- Performance: Consistent performance levels as more devices and users are added.
- Resource management: Efficient use of resources to ensure smooth operation during increased loads.
- Customizability: Flexibility to adapt the solution to meet changing business needs.
Importance of Automation and Autonomous Response
Automation significantly enhances the efficiency of cybersecurity tools by reducing the need for manual intervention. Features that facilitate this include:
- Automated incident response: Tools should be able to take predefined actions when a threat is detected.
- Continuous monitoring: The ability to scrutinize activities in real-time without requiring human oversight.
- Self-tuning capabilities: Adjustments to algorithms based on operational feedback to optimize performance.
Leading AI Cybersecurity Platforms and Their Use Cases
In the rapidly evolving landscape of cybersecurity, several platforms have emerged as leaders in leveraging AI technologies to protect against sophisticated threats. These tools offer varied capabilities tailored to enhance organizational security across multiple domains.
Application Security and Software Supply Chain Protection
Addressing vulnerabilities in application security and the software supply chain is critical as cyber threats become more intelligent. AI-driven platforms are redefining how organizations manage these risks.
Managing Security Posture in ASPM and AppSec
Application Security Posture Management (ASPM) tools provide a comprehensive view of security risks throughout the software development lifecycle. They automate the assessment of applications, ensuring compliance with security policies while identifying vulnerabilities in real time. By employing machine learning algorithms, these tools can prioritize risks based on potential impact and exploitability, enabling development teams to address critical issues more efficiently.
Securing Software Supply Chains with Machine Learning
Machine learning enhances the security of software supply chains by analyzing patterns and detecting anomalies in third-party components. This proactive approach identifies potentially malicious components before they can be integrated into production environments. Continuous monitoring ensures that organizations remain compliant and secure as new threats evolve.
Endpoint Detection and Response Solutions
Endpoint detection and response (EDR) solutions have shifted from traditional methods to incorporate AI and machine learning for better threat mitigation.
Real-Time Threat Detection Across Networks and Devices
AI-powered EDR tools offer real-time visibility into endpoint activities. Utilizing behavioral analytics, these solutions can detect unusual patterns indicative of potential threats, enabling rapid response to incidents. This proactive monitoring minimizes the risk of breaches by spotting threats before they escalate.
Automated Incident Response for Malware and Ransomware
Automated incident response significantly reduces the time taken to address malware and ransomware attacks. By leveraging AI, these systems can initiate containment procedures and remediate threats without human intervention. This swift action limits damage and enhances overall resilience.
Cloud Security and Risk Management
In the cloud-centric world of 2026, organizations face unique challenges in securing their cloud infrastructure. AI tools provide critical support in managing these complexities.
Continuous Compliance and Risk Analysis for Cloud Workloads
AI-driven cloud security platforms ensure continuous compliance with industry standards by providing real-time risk analysis. They automatically assess cloud configurations and workloads, identifying deviations that could expose the organization to threats.
Managing Permissions and Exposure in Cloud Environments
Effective permission management is essential for protecting cloud assets. AI solutions analyze user behavior and adjust permissions accordingly, ensuring that access is granted only to authorized individuals while monitoring for any suspicious activities.
AI Models and Machine Learning Techniques in Cybersecurity
AI and machine learning are pivotal in shaping the future of cybersecurity. These technologies enhance the ability to identify and respond to threats by leveraging complex algorithms and data analysis.
Behavior-Based Detection of Suspicious Activities
One of the most significant advancements in AI-driven cybersecurity is behavior-based detection. This approach monitors user and system activities to establish a baseline of normal operations. By analyzing patterns, it can identify deviations indicative of potential threats. Behavioral analytics is especially effective in detecting sophisticated attacks that traditional signature-based systems may overlook, such as insider threats and advanced persistent threats (APTs).
Learning from Past Incidents to Predict Emerging Threats
Machine learning models utilize historical incident data to recognize trends and predict future threats. By examining previous breaches and attack vectors, these models become adept at identifying anomalies. This predictive capability allows organizations to preemptively bolster their defenses, adapting strategies based on calculated threats and emerging attack patterns.
Use of Large Language Models and Prevention of LLM Injection Attacks
Large Language Models (LLMs) have been incorporated to enhance security measures against various forms of cyber attacks. They can analyze interactions within applications and communication channels to detect abnormal requests. By employing LLMs, organizations gain a robust layer that assists in preventing injection attacks, especially those targeting AI systems themselves.
Autonomous Learning and Adaptive Security Posture Management
Autonomous learning capabilities allow AI systems to continuously evolve their defenses without human intervention. Such systems utilize feedback loops from both successful and thwarted attacks to refine their models. Adaptive security posture management leverages this continuous learning process, enabling systems to adjust their policies and responses based on real-time threat intelligence and changing environments.
Enhancing Security Teams with AI and Automation
The integration of AI and automation is revolutionizing security teams, transforming their capabilities and approaches toward threat management. By leveraging these advanced technologies, organizations can bolster their defenses and streamline operations.
Reducing Manual Workload through Automated Threat Detection
Automated threat detection powered by AI significantly decreases the burden on security teams. This technology allows for the continuous monitoring of systems, enabling faster identification of vulnerabilities and potential breaches. Key benefits include:
- Real-time alerts on suspicious activities, reducing the time for response.
- Automation of routine monitoring tasks, freeing analysts to focus on more complex challenges.
- Enhanced accuracy in threat detection by leveraging machine learning algorithms to discern between normal and anomalous behavior.
Augmenting Human Teams with AI-Driven Cybersecurity Analysts
AI-driven tools can act as force multipliers for human analysts, enhancing their decision-making capabilities. These systems provide insights derived from vast datasets, enabling security personnel to make informed choices quickly. AI support includes:
- Predictive analytics to identify emerging threats before they materialize.
- Contextual information surrounding alerts, allowing analysts to prioritize incidents effectively.
- Guidance on potential patching or remediation steps based on similar past incidents.
Limitations of AI and the Need for Human Oversight
While AI offers remarkable efficiency, its limitations necessitate human oversight. Automated systems can sometimes generate false positives, requiring human judgment for accurate assessment. Issues include:
- The potential for machine errors that could lead to missed threats if relied upon exclusively.
- The necessity to interpret complex situations where nuanced human understanding is essential.
- Maintaining ethical considerations in decision-making, which must involve human input to navigate sensitive scenarios.
Automated Red Teaming and Continuous Security Testing
Automated red teaming uses AI to simulate attacks, providing continuous testing of security systems under real-world scenarios. This proactive approach helps organizations identify weaknesses and strengthen their defenses. Benefits of this methodology include:
- Constant evaluation of security measures, helping teams stay one step ahead of potential threats.
- Realistic assessment of incident response effectiveness in dynamic environments.
- The generation of actionable insights for improving security protocols based on simulated breaches.
Addressing Specific Threats with AI-Powered Tools
In today’s dynamic threat landscape, leveraging AI-powered tools is crucial for effectively addressing specific cybersecurity challenges. Below are key strategies employed to mitigate various forms of cyber risks.
Mitigating Phishing and Social Engineering Attacks
AI technology plays a vital role in counteracting phishing and social engineering threats. These sophisticated attacks often exploit human psychology, making traditional defenses inadequate. AI-driven systems enhance email filtering and prevent deceptive communications by:
- Analyzing the context and language of emails to detect anomalies.
- Employing machine learning models that adapt continuously based on emerging phishing trends.
- Utilizing behavioral analysis to flag accounts engaging in suspicious activities.
By recognizing patterns in data, AI tools can proactively disarm threats before they reach end-users, thereby strengthening overall security postures.
Early Detection and Response to Malware, Ransomware, and Zero-Day Threats
The rapid identification of malware and ransomware is critical. AI-powered tools implement various methods to enhance early detection, which is essential in minimizing damage. These include:
- Utilizing real-time monitoring to analyze file behaviors and detect anomalies.
- Employing heuristics and machine learning to identify zero-day vulnerabilities.
- Implementing automated response protocols that isolate infected systems immediately.
This proactive approach not only minimizes disruption but can also prevent data breaches from occurring.
Real-Time Monitoring to Prevent Supply Chain Security Breaches
Supply chain vulnerabilities have become a primary target for cybercriminals. Employing AI tools facilitates real-time monitoring and broader visibility across complex networks. Key actions include:
- Conducting continuous risk assessments on third-party vendors.
- Establishing secure connections that analyze data flows for unauthorized transmission.
- Detecting unusual activities that may indicate a supply chain compromise.
With these strategies, organizations can maintain robust security measures across their supply chains and respond quickly to potential risks.
Integrating AI Cybersecurity Solutions Across Enterprise Environments
Integrating AI-powered cybersecurity solutions into enterprise environments is crucial for defending against a wide array of cyber threats. The effectiveness of these solutions hinges on their compatibility with existing systems and their ability to manage security seamlessly across various platforms.
Compatibility with CI/CD Pipelines for Secure Development
Ensuring that AI cybersecurity tools can effectively integrate with Continuous Integration and Continuous Deployment (CI/CD) pipelines is essential. Organizations adopting DevSecOps practices benefit from this integration by embedding security measures throughout the development lifecycle.
- Real-time security checks can be automated within the CI/CD process.
- Vulnerabilities can be detected earlier, reducing the likelihood of deploying insecure code.
- Automated compliance audits can help ensure that all deployed applications adhere to security standards.
Managing Security Across Hybrid Cloud and On-Premises Systems
In 2026, many organizations utilize a hybrid approach, combining on-premises infrastructure with cloud services. This complexity requires cybersecurity solutions that can operate effectively across both environments.
- AI tools should provide unified visibility, allowing for centralized monitoring of both cloud and on-premises resources.
- Security policies must be consistent and enforceable across all platforms to prevent loopholes.
- Automated workflows can enhance incident response capabilities in real-time.
Ensuring Data Integrity and Traceability with Emerging Technologies
Data integrity is paramount in maintaining trust and security. Emerging technologies such as blockchain can be integrated with AI cybersecurity solutions to enhance both data integrity and traceability.
- Blockchain technology can provide an immutable ledger of transactions, allowing organizations to validate data movements.
- AI can analyze patterns and anomalies in data flows, providing insights that help to preempt security breaches.
- Organizations benefit from improved audit trails, making compliance with regulations easier and more transparent.
Future Trends in AI Cybersecurity for 2026 and Beyond
The landscape of AI cybersecurity is rapidly evolving, especially as organizations aim to mitigate increasingly sophisticated threats. This section explores the future trends set to shape AI-driven cybersecurity solutions in the coming years.
Advanced Machine Learning Models for Improved Threat Detection
As the complexity of cyber threats increases, organizations are turning to advanced machine learning techniques that leverage vast datasets for better threat detection. These models are designed to recognize patterns and anomalies more quickly and accurately than their predecessors. Key advancements include:
- Real-time analysis of network traffic to identify suspicious behavior.
- Enhanced model architectures that improve predictive capabilities.
- Incorporation of unsupervised learning for adaptive responses to unknown threats.
Blockchain Integration for Enhanced Data Security in Cyber Defense
Blockchain technology is emerging as a robust solution to enhance data security. By utilizing its decentralized nature, businesses can provide superior integrity and transparency for their digital information. Key aspects include:
- Immutable record-keeping for data transactions, which boosts trust.
- Decentralization that reduces vulnerability to single points of failure.
- Smart contracts that automate compliance and access control processes.
Securing AI and Machine Learning Models Themselves
With an increasing reliance on AI and machine learning, securing these models has become essential. Protecting AI models from adversarial attacks and data poisoning will be paramount. Relevant measures include:
- Implementing robust access controls to limit model exposure.
- Regular audits and updates to ensure model integrity.
- Adopting techniques to detect and mitigate adversarial inputs.
Preparing Security Teams for AI-Driven Threat Landscapes
Lastly, enhancing the skills of security teams is critical for navigating the evolving threat landscape. Training programs focusing on AI technologies will equip teams with necessary competencies, including:
- Understanding the principles of machine learning and AI applications in security.
- Developing strategies for collaboration between AI-driven tools and human expertise.
- Creating frameworks for continuous learning and adaptation in a dynamic environment.


